- High Speed, Contactless (RFID/NFC) Interface ISO 14443
- Powered by CardLogix’ M.O.S.T. Operating System
- Up to 92k Bytes of EEPROM / User Memory
- Cyclical, Linear, and Purse File types
- Secured E-Purse/ E-Payments
- Injectable AES Keys with Admin Password
- Special transport keys for lifecycle control
- SHA-1 for mutual authentication
- Extended file sizes that breaks the 32k Bytes barrier set by ISO
C6 – M.O.S.T. Card® Contactless Microprocessor Smart Cards
Description
CardLogix M.O.S.T. Card® C6 Series is a contactless microprocessor smart card family built on CC EAL5+ certified silicon and powered by the M.O.S.T. Card Operating System. The smart cards are designed for multi-function and/or high security applications. The C6 family features up to 92k bytes of user memory that can be configured for a wide variety of applications including access control, single sign-on (SSO), session key-based purse functions, and contactless badging with on-card biometric storage.
The M.O.S.T. C6 Card series features advanced password security logic, 3DES and AES encryption, SHA1 hashing and authentication, and flexible file management. Its 24 byte global unique identifier (GUID) makes the credential truly unique. The silicon provides continuous internal encryption of all data and the virtualization and rotation of the data across the non-volatile memory for secure data storage. The M.O.S.T. OS also features an error detection code and security self-tests with built-in anti-tearing mechanisms to support heavy transactional environments.
The C6 series offers injectable AES keys and an Administrator Password for organizations that need to update their systems during the cards’ useful life without the need to re-issue all credentials. It supports EF-level PIN/passwords, multiple file types, and it includes an internal random number generator for unique transaction sessions.
CardLogix M.O.S.T. Toolz™ SDK lets you design a system that grows with your needs. M.O.S.T. Card is future-proofed while working on multiple silicon vendors’ devices, so your projects will always be supported. M.O.S.T. Cards enable multiple applications on a single card, and they are a mission critical component of the infrastructure to keep your system safe. Build confidence in your chain of trust with proven smart card technology and CardLogix services.
Specs
General Features
- Operating voltage range: 1.62V to 5.5V (ISO 7816 Class A, B, and C)
- CRC16 and CRC32 engines are compliant with ISO/IEC 3309
- Global unique card identifier system (GUID) is compliant with ASN.1 Object Identifier components (ITU-T Rec. X.667 | ISO/IEC 9834-8, and with IETF RFC 4122)
- Conforms to FIPS 197
- Authentication mechanisms are fully compliant to Secure Hash Standard (SHS) FIPS PUB 180-4
- Conforms to (HDLC) procedures ISO/IEC 13239:2002
- Programmable passwords for all access modes: read, write, update, invalidate and rehabilitate
- Data retention > 10 years
- Endurance: maximum of 16.5 million programming cycles at 25° C
- Electrostatic discharge protection > 6,000V
File Support
- Master File (MF)
- Directory File (DF)
- EF Transparent File
- EF Large File Size
- Linear & Cyclical Files
- Purse Files
- APP & CHV Password Files
- Master CHV File
- Admin Password with Injectable AES Keys
Encryption/ Authentication
- SHA-1
- 3DES
- AES-128
High-Security Architecture
- A wide variety of user memory sizes
- T= ISO 14443 A & B
- PC/SC compatible
- Negotiable communication speed (PTS)
- Rapid card development through M.O.S.T. Toolz
- Multiple reader and terminal choices
- ISO 7816 1-4 and ISO 14443A compliant
Dedicated Semiconductor and Operating System Countermeasures Guard Against:
- Side channel attacks
- Advanced fault attacks
- Velocity checking
- Voltage attacks
- Frequency attacks
- Temperature glitch attacks
- Optical attacks
Custom Card Security Options
- Laser engraving/indenting
- Guilloche and rosettes
- Microprinting
- Optically Variable Devices (OVDs) and holograms
- Hidden Card Validator™ graphics with lens viewer
- Ultraviolet (UV) ink
- Watermark
- SBumps
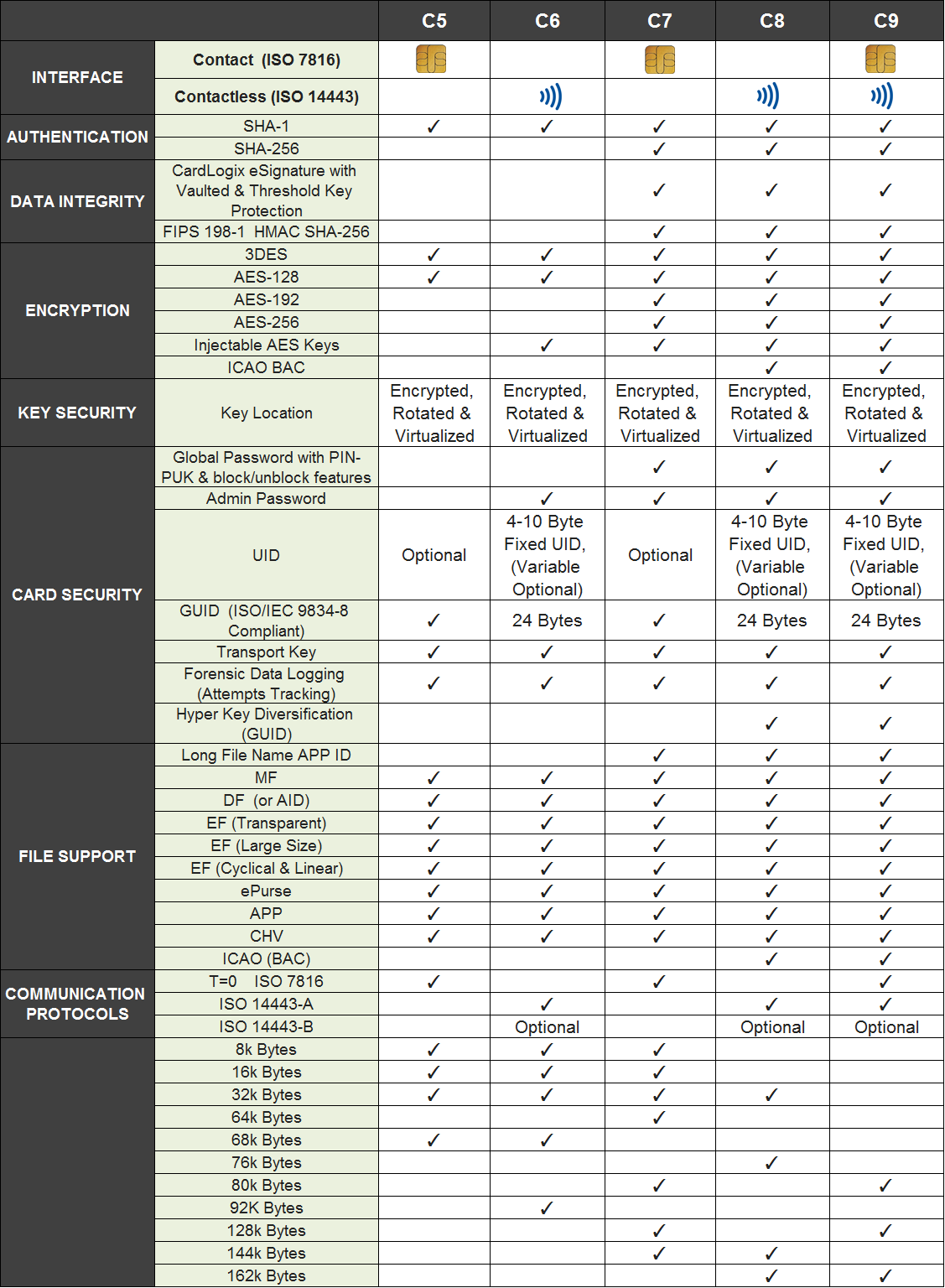
Compare
M.O.S.T. Card C Series | Features Comparison (C5, C6, C7, C8, C9)
Features
Smart Alternative to MIFARE, ProxCard and iClass Cards
The M.O.S.T. Card C6 gives you a robust contactless (RFID) interface backed by an intelligent operating system and microprocessor with more available user memory, more advanced encryption algorithms, and more security features than a MIFARE, ProxCard (Proximity cards), or iClass card—all at a lower cost to the end user. The M.O.S.T. Card C6 leverages the Advanced Encryption Standard (AES) for data encryption, the strongest encryption algorithm to date, so that your data will remain 100% confidential no matter where it is transmitted. AES has typically been found on card operating systems that support public key infrastructure, but now users can get PKI security at the price of a contactless symmetric key card.
High Security Architecture — Powered by the M.O.S.T. Card® Operating System
The M.O.S.T. Card C6 is powered by CardLogix’ proprietary M.O.S.T Card Operating System which supports a variety of security measures, including SHA-1 bi-directional / mutual authentication, AES, DES, and 3DES, PIN/passwords, and internal random number generation for unique e-signatures and transaction sessions. The OS is built with an error detection code and security self-tests. The EAL certified silicon provides continuous encryption of all data and the virtualization of the data across the non-volatile memory.
Large EEPROM Storage Capacity — Up to 68k Bytes
The M.O.S.T. Card C6 family offers up to 68k bytes of user memory. The large storage capacity increases the card and password functionality, enabling multiple applications on one card, and substantially increasing security. The C6 family allows a user to safely store and transmit a large amount of personal and sensitive data contactlessly, including biometric information —data too vulnerable to manage over a loosely protected network. The M.O.S.T. Card C6 is capable of managing card holders’ and card issuers’ data on the card so that physical access controls systems, loyalty, e-payment and in-the-field civil ID, national ID and military identification programs can benefit from a secure closed system that does not rely on being connected to a network at all times.
Multiple Applications On One Card for Better Cost-Efficiency
With the M.O.S.T. Card C6, your organization can benefit from the economies of scale achieved by using one card for multiple purposes. Why settle for a single-purpose memory card like the iClass or ProxCard when a company can combine a physical access control system (PACS), customer loyalty program, multi-factor identification, e-payment system, single sing on, and player/ customer tracking onto one company-branded M.O.S.T. Card for the same price or less as a memory card? Improve your organization’s security by arming your employees with the M.O.S.T. Card to handle multi-factor authentication and non-refutable identification. Use the same card to control facility access rights, to institute an employee incentive program, and to protect classified or sensitive data. The application possibilities are endless, and the M.O.S.T. Card C6 can handle it all to meet any of your organization’s needs.
Admin Password & Injectable AES Keys — Ideal for PACS System Management
During the design phase of the M.O.S.T. Card C6, using M.O.S.T. Toolz™ Card Configuration Utility, the card issuer creates an Administration Password File, protected by a password that cannot be accessed or changed after construction. With the Admin Password File, an authorized security systems control manager can add injectable AES Keys should door locks be changed or should any password modifications be needed. This allows the manager the flexibility to safely update his or her physical access control system without having to re-issue cards.
Rapid Smart Card System Development for Flexible and Easy-to-Build Card Applications
CardLogix has provided a complete line of user-friendly development tools to create both custom and pre-configured smart card applications. Project development for the M.O.S.T. Card C6 is supported by the PCSC API and the M.O.S.T. Toolz™ Card File Creation Utility SDK, including the powerful Winplex® API. The M.O.S.T. Toolz File Creation Utility features an intuitive user-interface that allows a card issuer the flexibility to design a M.O.S.T. Card file structure and set passwords that fit the needs of any custom smart card program. M.O.S.T. Toolz also provides intelligently constructed, pre-configured idblox™ applications cards, leveraging the M.O.S.T. Card Operating System. With this option, a card issuer’s only job is to setup passwords. Smart card development could not get any easier.
Eliminate the need to hire a graphic designer by starting with one of CardLogix’ professionally designed, pre-printed ReadyStart™ Secure Cards or Holofoil Cards, with embedded 2D holograms. Both use high security graphic printing technology that provides additional levels of physical security to your M.O.S.T. Card®
True Software and Hardware Interoperability — idblox™ Compatible
The M.O.S.T. Card C6 family is future-proofed, working on multiple silicon vendors’ devices so that your projects are always supported. The card family is part of the idblox™ ecosystem which has attracted multiple vendors for compatible smart card readers, smart card terminals, smart card applications and all other smart card infrastructure components. The idblox ecosystem leverages a unique methodology that enables true card system interoperability without requiring programming.
Learn more about the idblox™ ecosystem, the only smart card ecosystem with true interoperability that enables the fastest, easiest and most affordable creation of high-security smart card programs for any card application.
Smart Card Personalization Made Easy — The Card Encoding Engine™
The M.O.S.T. Card family is supported by the latest innovation in smart card personalization — The Card Encoding Engine™. The Card Encoding Engine is the first of its kind to offer smart card encoding without requiring programming first in order to do so. This revolutionary software engine is the cornerstone of idblox, allowing inline creation of a smart eID card program from design to use without relying on programmers.
Seamless Biometric Enrollment and Card Issuance of Biometric Smart Cards
CardLogix is strategically partnered with Corvus Integration, Inc., experts in biometric enrollment and biometric verification technologies, to bring you the simplest way to register personnel’s biometric information and load it onto a smart card within minutes. Biometric data combined with a smart card provides the highest security and protection of personnel, data and valuable assets. With the M.O.S.T. Card C6, your organization can benefit from this level of security without having to spend more money than it’s worth.
Development
M.O.S.T. Toolz™ SDK
Rated “Most comprehensive and professional SDK for smart card system developments”, MOST Toolz is designed for multi-function and high security smart card systems. M.O.S.T. Toolz™ is an affordable SDK and Card Configuration Utility for developing the M.O.S.T. Card® and other microprocessor smart cards. High level commands are sent through the Winplex® API to the card reader, which is included in the M.O.S.T. Toolz kit. M.O.S.T. Toolz enables programmers to create a smart card-based transaction system that updates and secures files while setting a variety of defensive measures to protect user ID, card access, and file information. CardLogix gives you the power to deliver multiple products and services on a single card, allowing for fast system design and easy updating without the need for card re-issuance.

MOST Smart Card Development
Applications
- Loyalty Cards
- Healthcare (EMR)
- Ticketing
- Cashless Vending
- Gaming
- Public Transit
- e-Banking
- Identity
- Charging the money card (e-purse)
- Enterprise Badging
- e-Passport personalization & verification
- PKI (public-key infrastructure) Applications
- e-Commerce (online payment)
- Secure network access
- Hospitality
- Electronic voting
- Computer security (log in access)
- Energy Management
- Border Crossing
- Customs
- Access Control System
- Time and attendance System
- Hazmat Cards
- Set-Top Cards
- Debit Cards, ATM Cards, Credit Cards
- Driving License
- Petrol Card
- National ID Cards
- NFC Payment
Manufacturer
Corporate Profile
CardLogix is an ISO 9001:2016-certified smart card manufacturer, software developer, and the premier provider of smart card technology with a comprehensive line of SDKs and tools that enable easy and rapid development of high quality smart cards. Since 1998, CardLogix has supplied millions of cards and card components to over 42 countries around the world. As an expert in smart card and chip technology, card operating systems, card software, development tools, and middleware, CardLogix has continuously been at the forefront of smart card technology.
CardLogix’ Mission
CardLogix’ mission is to make highly secure, high quality smart card systems more widely available to customers in need. CardLogix strives to make data transactions more secure, personnel and assets more protected, and to turn otherwise complex and expensive smart card systems into simpler, more cost-effective, and easier-to-develop solutions for everyone.
CardLogix Values
Trust is the primary commodity that CardLogix trades in every day. CardLogix builds and maintains customers’ confidence their products and processes, so that they can trust our cards to reliably protect personnel, sensitive data, and their most valuable assets. Starting with development software that’s flexible and easy to use to uncompromising customer support, CardLogix delivers on the promise of trust that our service inspires and our cards guarantee. Our company culture breeds initiative, commitment, and follow-through. As a global supplier and active industry participant, CardLogix understands the importance of being a responsible global business. With recycling, energy conservation, and full RoHS compliance, the company meets its goals with the environment in mind.
CardLogix Advantage
- Experts in smart card technology with an understanding of what it takes to get a card project from A to Z
- Commitment to ISO, ICAO, and industry conformance to ensure performance and interoperability
- Extensive partnerships with companies that offer complementary smart card infrastructure components
- Innovative products and solutions that simplify smart card development
- Cutting edge technology, sophistication and differentiated quality at a fraction of competitors’ costs
- Continuous customer support and involvement with evolving card projects
CardLogix Solutions
CardLogix manufactures high security and multi-functional ISO compliant smart cards, powered by CardLogix’ own operating systems. CardLogix offers easy-to-use SDKs for programmers, powerful middleware and APIs, a variety of applications software, and innovative solutions that empower end-users to develop and personalize smart cards without requiring any user-programming. The company partners with key suppliers in software, biometric capture, readers, and printers to deliver complete, leading-edge solutions. CardLogix smart card platforms provide solutions for multiple applications to markets globally, such as national, civil, voter and enterprise identity; physical and logical access cards; stored value; loyalty and rewards programs; e-purse; gaming, healthcare and other solutions that use a combination of multiple applications onto one card.
Definitions
- AES (Advanced Encryption Standard)
- A symmetric 128-bit block data encryption technique developed by Belgian cryptographers Joan Daemen and Vincent Rijmen. The U.S government adopted the algorithm as its encryption technique in October 2000, replacing the DES encryption it used. AES works at multiple network layers simultaneously. The National Institute of Standards and Technology (NIST) of the U.S. Department of Commerce selected the algorithm, called Rijndael (pronounced Rhine Dahl or Rain Doll), out of a group of five algorithms under consideration, including one called MARS from a large research team at IBM.
- Anti-tearing
- A card feature which protects the contents of memory if the card is removed before the end of the transaction.
- API (Application programming interface)
- A source code interface that a computer system or program library provides to support requests for services to be made of it by a computer program. An API differs from an application binary interface in that it is specified in terms of a programming language that can be compiled when an application is built, rather than an explicit low level description of how data is laid out in memory.
- CHV
- Cardholder Verification
- Contactless Card
- A proximity card (prox card or RFID card) is a generic name for contactless integrated circuit devices used for security access or payment systems. The card contains electronic information that can be read from a distance with special card readers that use radio wave. The card It can refer to the older 125 kHz devices or the newer 13.56 MHz contactless RFID cards, most commonly known as contactless smartcards.
- DES (Data Encryption Standard)
- A widely-used method of data encryption using a private (secret) key that was judged so difficult to break by the U.S. government that it was restricted for exportation to other countries. There are 72,000,000,000,000,000 (72 quadrillion) or more possible encryption keys that can be used. For each given message, the key is chosen at random from among this enormous number of keys. Like other private key cryptographic methods, both the sender and the receiver must know and use the same private key.
- EEPROM
- A memory chip that can be reprogrammed any number of times, as to correct bugs, by first clearing its contents with ultraviolet light.
- Electronic Health Record (EHR or EMR)
- An electronic health record is a collection of patient health information generated by one or more meetings in any care delivery setting. An EHR typically includes patient demographics, progress notes, problems, medications, vital signs, past medical history, immunizations, laboratory data and radiology reports. It’s said to streamline clinicians’ workflow, and it has the ability to generate a complete record of a clinical patient encounter.
- E-purse (electronic purse)
- A smart card can be used to store a monetary value for small purchases. Card readers retrieve the amount currently stored, and subtract the amount for the goods or services being purchased. Groceries, transportation tickets, parking, laundromats, cafeterias, taxis and all types of vending machines are only some of the purchases that often do not reach amounts to justify the hassle of using a credit card (a cash card reader does not require a permanent phone connection with a host computer). Radio-read smart cards will allow the free flow of people through transportation systems, avoiding the need of ticketing machines or validation gates.
- FIPS (Federal Information Processing Standards)
- A set of standards that describe document processing, encryption algorithms and other information technology standards for use within non-military government agencies and by government contractors and vendors who work with the agencies.
- GUID (Global Unique Identifier)
- A unique reference number used as an identifier in computer software. The term GUID typically refers to various implementations of the universally unique identifier (UUID) standard. A smart card can register support for an interface through association with the interface’s (GUID). This binding between a card and an interface is done at the time the card is first introduced to the system&emdash;typically when the SCSP is installed. Once the card is introduced to the system, applications can search for smart cards, based on a specific interface or GUID. For example, a cash card could make itself available to Windows-based applications by registering interfaces to access its purse scheme.
- ISO
- Founded in 1946, ISO is an international organization composed of national standards bodies from over 75 countries. For example, ANSI (American National Standards Institute) is a member of ISO. ISO has defined a number of important computer standards, the most significant of which is perhaps OSI (Open Systems Interconnection), a standardized architecture for designing networks.
- ISO/IEC 7810
- The standard specifies the physical characteristics of identification cards including card material, construction, characteristics and nominal dimensions for three sizes of cards (ID-1, ID-2 and ID-3). It is the ID-1 card that forms the basis of ISO 7816-1.
- ISO/IEC 7816
- The standardization of physical characteristics, dimensions and location of contacts, electrical interface and transmission protocols, organization, security and commands for interchange of a smart card. It was created in 1987, updated in 1998, amended in 2003.
7816 Specifies:
- Contents of command-response pairs exchanged at the interface
- Means of retrieval of data elements and data objects in the card
- Structures and contents of historical bytes to describe operating characteristics of the card
- Structures for applications and data in the card, as seen at the interface when processing commands
- Access methods to files and data in the card
- A security architecture defining access rights to files and data in the card
- Means and mechanisms for identifying and addressing applications in the card
- Methods for secure messaging
- Access methods to the algorithms processed by the card. It does not describe these algorithms
The characteristics specified include:
- Physical dimensions
- Resistance to bending, flame, chemicals, temperature and humidity
- Toxicity
- The standard includes test methods for resistance to heat
- Microprocessor
- A chip that serves as the Central Processing Unit controlling a computer. It provides programmable intelligence.
- Microprocessor Smart Cards
- A smart card that has a microprocessor that includes components of this type of architecture including a CPU, RAM, ROM, and EEPROM. The operating system is typically stored in ROM, the CPU uses RAM as its working memory, and most of the data is stored in EEPROM. A rule of thumb for smartcard silicon is that RAM requires four times as much space as EEPROM, which in turn requires four times as much space as ROM.
- OS (Operating System or COS)
- The OS is the hardware-specific firmware that provides basic functionality as secure access to on-card storage, authentication and encryption. Only a few cards allow writing programs that are loaded onto the smart card – just like programs on a computer. This is a great way to extend the basic functionality of the smart card OS.
- PC/SC (Personal Computer/Smart Card)
- A specification for smart-card integration into computing environments. Microsoft has implemented PC/SC in Microsoft Windows 200x/XP and makes it available under Microsoft Windows NT/9x. A free implementation of PC/SC, PC/SC Lite, is available for Linux and other Unixes; a forked version comes bundled with Mac OS X.
- PKI (Public key infrastructure)
- Enables users of a basically unsecure public network such as the Internet to securely and privately exchange data and money through the use of a public and a private cryptographic key pair that is obtained and shared through a trusted authority. The public key infrastructure provides for a digital certificate that can identify an individual or an organization and directory services that can store and, when necessary, revoke the certificates. Although the components of a PKI are generally understood, a number of different vendor approaches and services are emerging.
- RFID (Radio-frequency Identification)
- The wireless non-contact use of radio-frequency electromagnetic fields to transfer data, for the purposes of automatically identifying and tracking tags attached to objects. The tags contain electronically stored information. Some tags are powered by and read at short ranges via magnetic fields (electromagnetic induction).
- Secure Hash Algorithm (SHA-1)
- A 160-bit hash function which resembles the earlier MD5 algorithm. This was designed by the National Security Agency (NSA) to be part of the Digital Signature Algorithm.
- SDK (Software Development Kit)
- A package of pre-written code that developers can re-use in order to minimize the amount of unique code that they need to develop themselves. SDKs can help to prevent unnecessary duplication of effort in a development community.
- T=0
- A character-level transmission protocol, defined in ISO/IEC 7816-3. T=0 requires 2 request/response pairs per command (send command and get response saying got command, then a command to get the response and then the actual response).
- 3DES (Triple DES)
- Triple DES is a minor variation of this standard. It is three times slower than regular DES but can be billions of times more secure if used properly. Triple DES enjoys much wider use than DES because DES is so easy to break with today’s rapidly advancing technology. This just serves to illustrate that any organization with moderate resources can break through DES with very little effort these days.